- Release Notes
- Introduction
- Installation
- SKFS Installation Checklist
- Standalone Installation
- Clustered Installation
- Dockerized Installation
- Install HAProxy Load Balancer
- Upgrading SKFS
- Upgrading to SKFS 4.16.0
- Upgrading to SKFS 4.15.1
- Upgrading to SKFS 4.15.0
- Upgrading to SKFS 4.14.0
- Upgrading to SKFS 4.13.2
- Upgrading to SKFS 4.12.0
- Upgrading to SKFS 4.11.0
- Upgrading to SKFS 4.10.0
- Upgrading to SKFS 4.9.0
- Upgrading to SKFS 4.8.0
- Upgrading to SKFS 4.7.0
- Upgrading to SKFS 4.6.0
- Upgrading to SKFS 4.5.0
- Back
- Simulating Node Failures
- Removal
- Back
- Administration
- Operations
- Security
- Operating System
- Policy
- SKFS Policy Module (PM)
- JSON Schema
- Minimal (Any Hardware Authenticator)
- Moderate (Specific Authenticators)
- Strict (All Biometric Devices)
- Strict (Android SafetyNet)
- Restricted (TPM)
- Restricted (Android)
- Restricted (Apple PassKey)
- Restricted (FIPS)
- MetaDataService (MDS)
- FIDO Policy Options
- Back
- Back
- Configuration
- CLI Tool
- FIDO Operations (skfsclient)
- Admin Operations (skfsadminclient)
- Ping SKFS (P)
- Get Policy (GP)
- Create Policy (CP)
- Update Policy (UP)
- Delete Policy (DP)
- Get Configuration (GC)
- Update Configuration (UC)
- Delete Configuration (DC)
- Update Username (UU)
- Get User Keys (GUK)
- Add ROR (AR)
- Get ROR (GR)
- Update ROR (UR)
- Update and disable ROR (UDR)
- Add DAL Target (ADT)
- Get DAL Target (GDT)
- Update DAL Target (UDT)
- Update DAL target and disable (UDTD)
- Add x509fingerprint (ADFP)
- Update x509fingerprint (UDFP)
- Update x509fingerprint and disable (UDFPD)
- Back
- Back
- SSO
- Back
- How To ...
- Add an Additional Server to the SKFS Cluster
- Create and add new alias
- Debug Replication Issues
- Manage FIDO Metadata Service (MDS)
- Manage Keystores or Certificates
- Manage DAL
- Manage ROR
- Manage SKFS Policy
- Manage SKFS Configuration
- Perform SKFS Operations
- Replace a Server in the SKFS Cluster
- Back
- Troubleshooting
- Standalone Node Troubleshooting Guide
- Clustered Node Troubleshooting Guide
- Error Codes and Their Meanings
- Solutions for Known Issues
- Certificate not found in truststore while Authentication in Discover
- CORS Missing Allow Origin or ERR_CERT_AUTHORITY_INVALID
- Json could not be parsed : Invalid 'request type'
- Json could not be parsed : Policy requires counter
- JWT CIP 192.168.x.xx does not match: [localhost]]]
- mysql binary does not exist or cannot be executed
- Remote server does not listen for requests on [localhost:4848]
- RPID Hash invalid - Does not match policy
- This security key doesn't look familiar. Please try a different one.
- Back
- Back
- Developer
- Sample Applications
- SKFS API
- Build SKFS from source
- Tutorial
- Discoverable Credentials
- Related Origins Requests (ROR)
- Digital Asset Links (DAL)
- Back
- Demos
- MFA Implementations
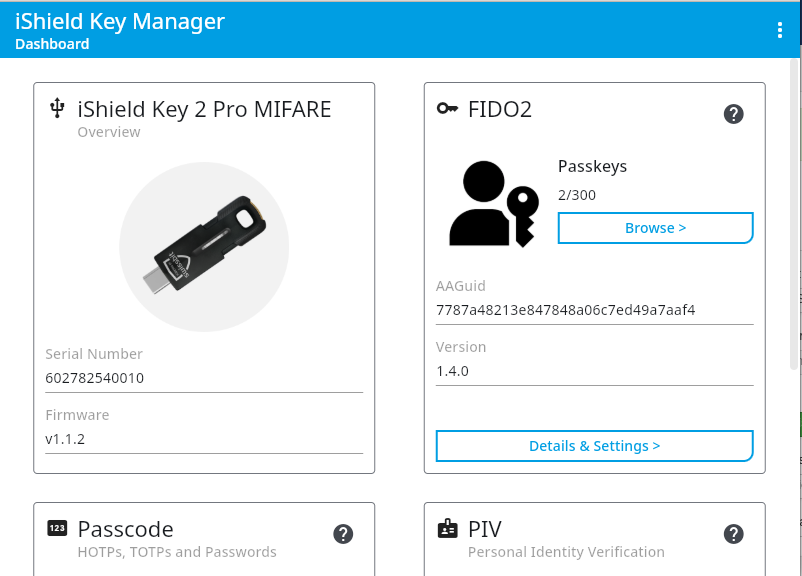
Configuring PAM for use with iShield Key 2
The following section describes how to configure the iShield Key 2 for use as a second factor to authenticating to a privileged credential on the Tellaro Console by assigning a PIN to it. This is only required if you want to enforce PIN for Linux login.
These steps were performed on a Rocky 10.1 computer; however, it is conceivable that the steps will be identical on all platforms supported by Swissbit. When performing this installation, the user must have Administrator privileges on the computer.
- Download the iShield Key Management Kit from Swissbit’s website.
- Install the downloaded software and run it as administrator.
- If you have not already inserted the iShield Key 2 into a USB slot on your computer, you will be prompted to insert one.
- You should see the iShield Key Management Kit’s Home screen – displaying the model name, firmware release number, as well as the serial number of the Security Key.
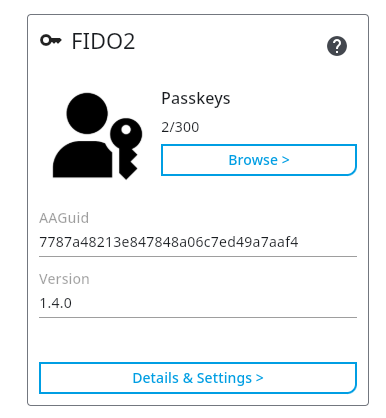
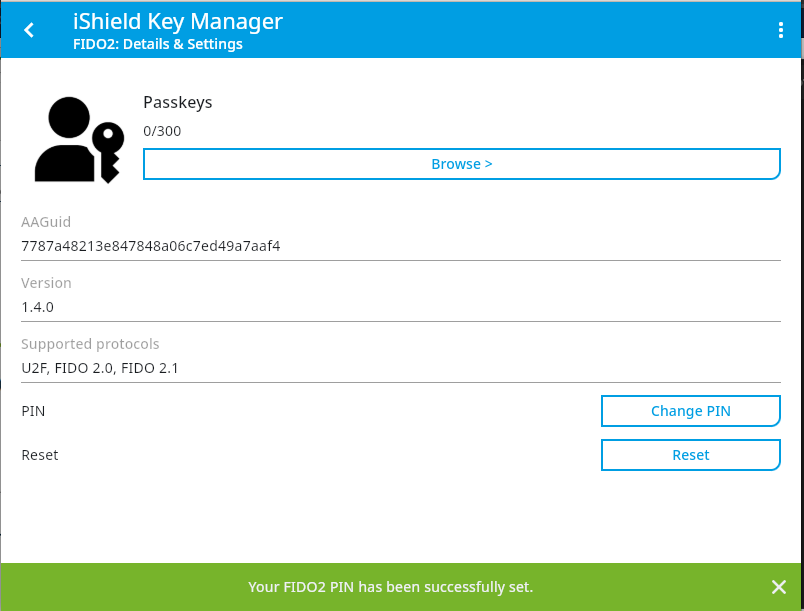
- Click on "Details & Settings" under the "FIDO2" section.
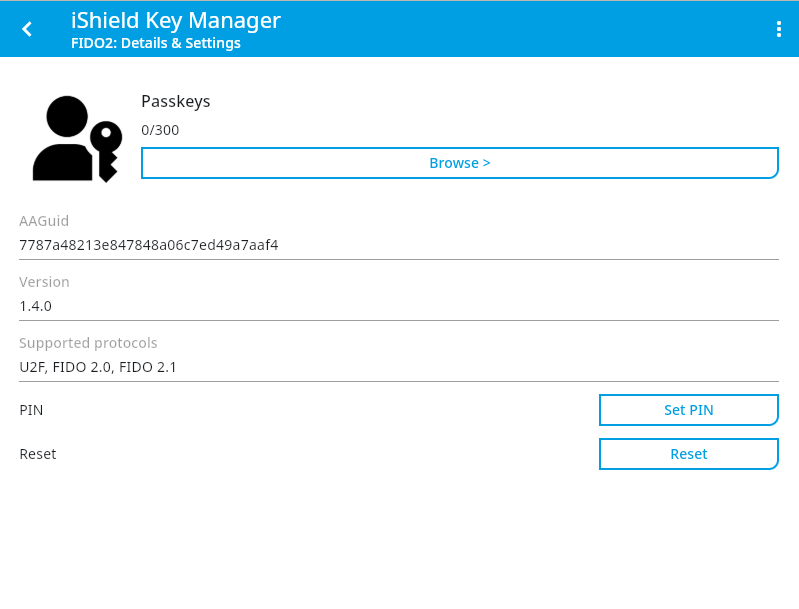
- You will be taken to a page where you can manage the FIDO2 PIN on the device. Click on "Set Pin".
- You will be prompted to set a PIN for the iShield Key 2. Enter a suitable PIN and click on "Set Pin".
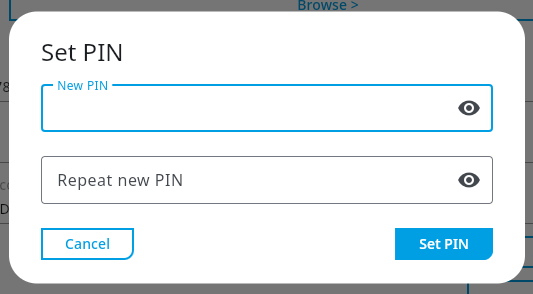
- Once the PIN is set, a message saying "Your FIDO2 PIN has been successfully set." will be displayed at the bottom of the application.
Copyright (c) 2001-2025 StrongAuth, Inc. (dba StrongKey) All Rights Reserved
